Coordinated, Automated and Efficient Incident Response
By integrating Mimecast with D3 Security, SecOps teams can standardize their incident response processes, execute repeatable tasks at scale, reduce the time it takes to detect and respond to email-borne attacks, making more efficient use of limited security resources. The D3 Security platform ingests rich Mimecast information for analyst investigation or automated playbook-driven response – from a single interface.


Solution Overview
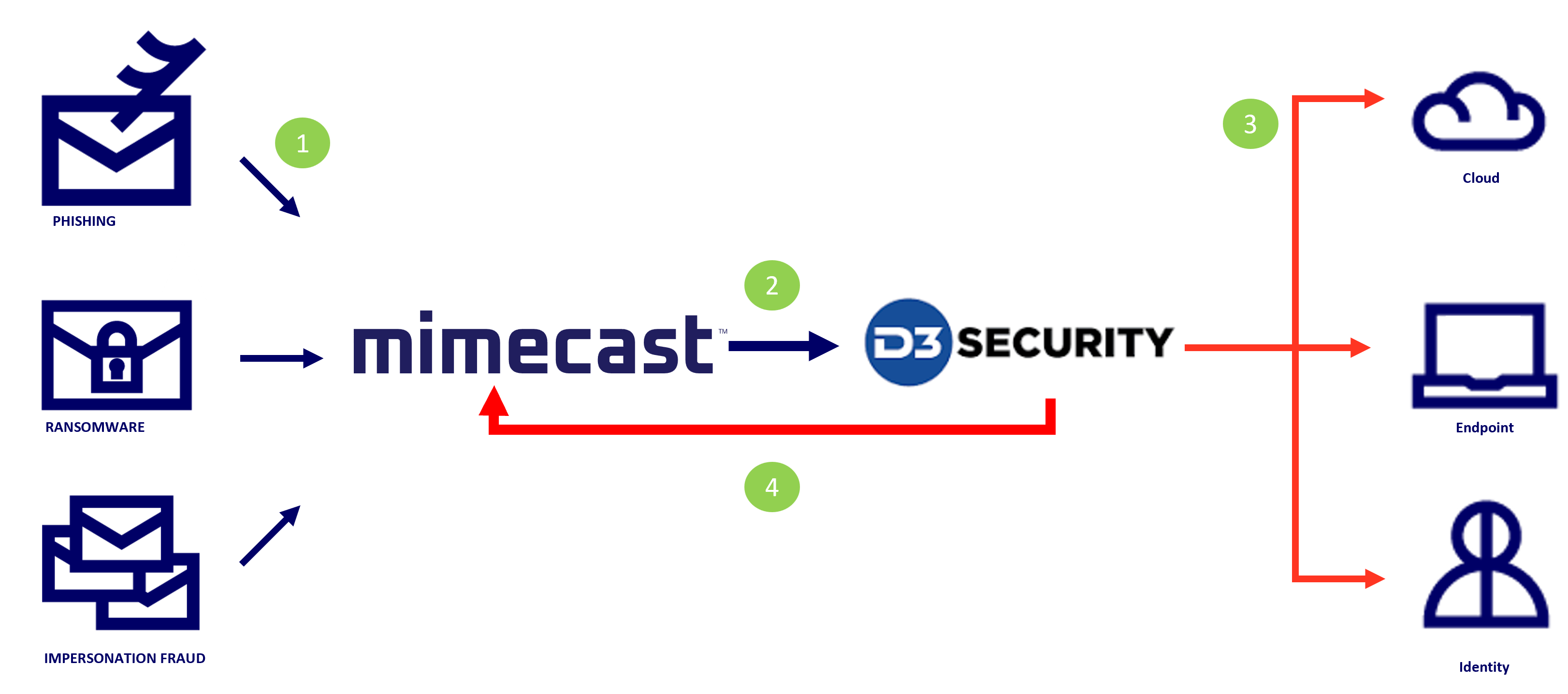
1. As inbound emails are received by Mimecast on behalf of the organization, they are subject to analysis by the Mimecast inspection funnel, where a series of email hygiene and advanced security scanning techniques are applied, to ensure that emails are safe before they are delivered to the recipient.
2. Email related data from Mimecast ingested into the D3 Security platform to help with analyst investigations.
3. Coordinate response actions across security tools based on Mimecast data.
4. Adjust Mimecast policies, search and destroy malicious emails, or prevent future threats.
Mimecast + D3 Security Use Cases:
Coordinated response aiding in:
Phishing Alert Enrichment and Response

Complex Email Threat Investigation

Alert Prioritization

Threat Intelligence





Key Benefits
01.
Automate email security processes, shorten decision making cycle, and drive resource efficiency through automation.
02.
Enrich intelligence from Mimecast and other security tools for coordinated response.
03.
Achieve full orchestration capabilities using proactive playbooks and workflows.