From Detection to Security Insights
By integrating Mimecast with LogPoint, organizations gain search and correlation capabilities across all log types to detect and respond to cyberattacks. Deep security insights and rich data visualizations cut cyberattack detection times and empowers incident response and threat-hunting teams to uncover the full kill chain to proactively find potentially malicious activity.


Solution Overview
1. Emails received by Mimecast are passed through a series of hygiene scanning techniques, to ensure that they are safe before delivery to the recipient.
2. Email intelligence provided by Mimecast is sent to LogPoint for normalization.
3. LogPoint uses the email intelligence to alert analysts and add context to data from other data sources.

Mimecast + LogPoint Use Cases:
Mimecast data ingested adds additional data and context within LogPoint to aid:
Automated Email Threat Enrichment

Complex Email Threat Investigation

Alert Prioritization

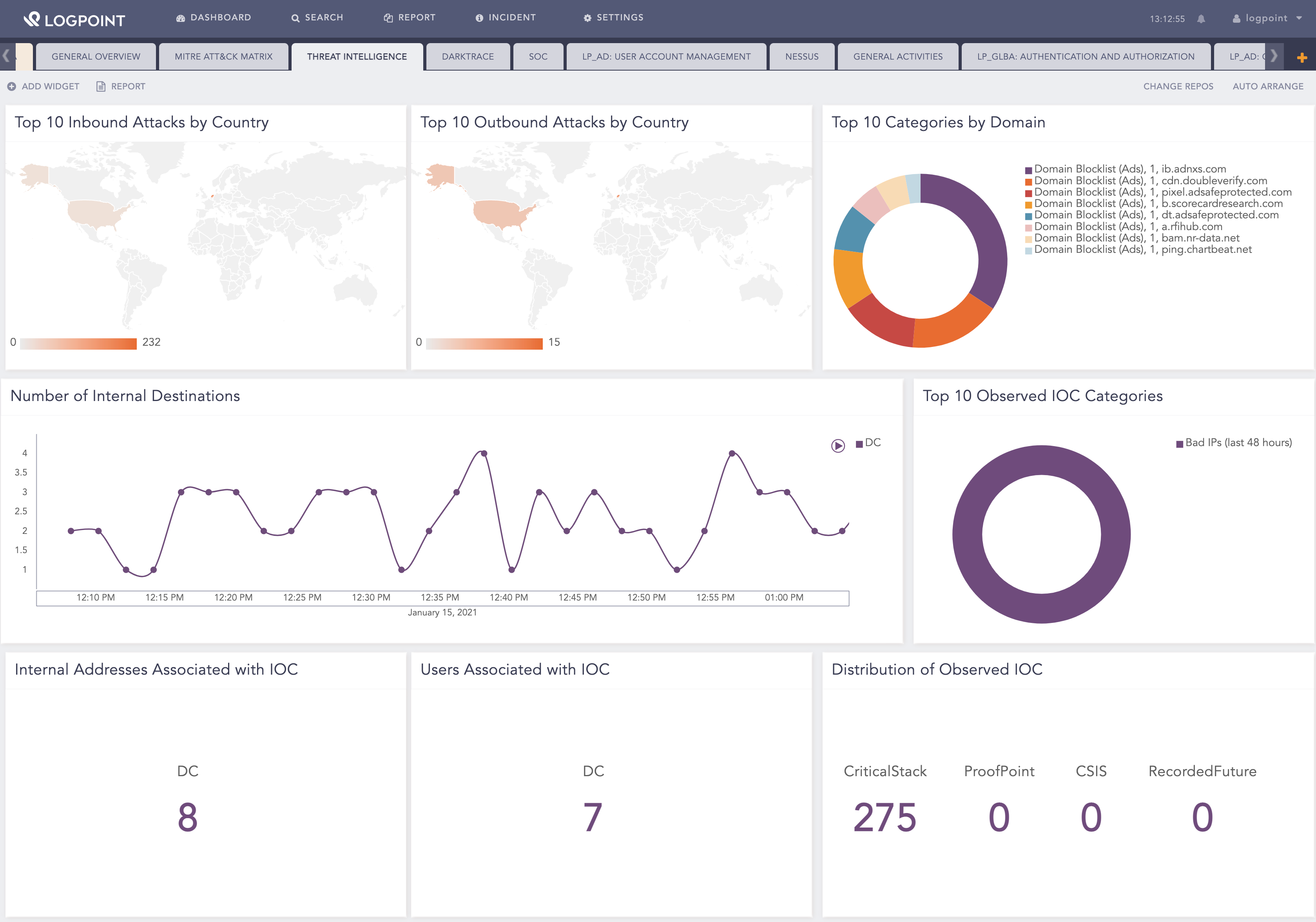
Threat Intelligence

Malware Containment

Phishing

Search and Destroy








Key Benefits
01.
Earlier detection and containment of attacks, with rapid response to phishing and business email compromise tactics.
02.
Threat intelligence enrichment detects threats within Mimecast events.
03.
Improve analysis and knowledge of threats through built in dashboards and Mimecast regional threat intelligence.
04.
Correlation across Mimecast events, cloud, endpoint, and network data to quickly identify high-risk individuals and devices that may create future security breaches.
05.
Shared intelligence identities the original threat and targets.