Advanced Threat Detection for Email and Cloud Applications
Mimecast and Netskope provide an integrated solution to improve detection, stop threats and increase organizational controls with integrated cloud platforms. By integrating Mimecast with Netskope, security teams can leverage advanced threat detection, enhanced investigations and faster response through proactive actions that identify at-risk users and devices. The integration enables bidirectional indicator of compromise sharing which automates the exchange of details about newly discovered customer-centric threats across different cloud platforms. This means that the attacks directed at the first entry point into an organization are shared across the other channels utilized, reducing the ability for a multi-vector attack to infiltrate.

Solution Overview
1. As inbound emails are received by Mimecast on behalf of the organization, they are subject to analysis by the Mimecast inspection funnel, where a series of email hygiene and advanced security scanning techniques are applied, to ensure that emails are safe before they are delivered to the recipient.
2. Any infected messages detected are not delivered to the intended recipient, protecting the organization immediately.
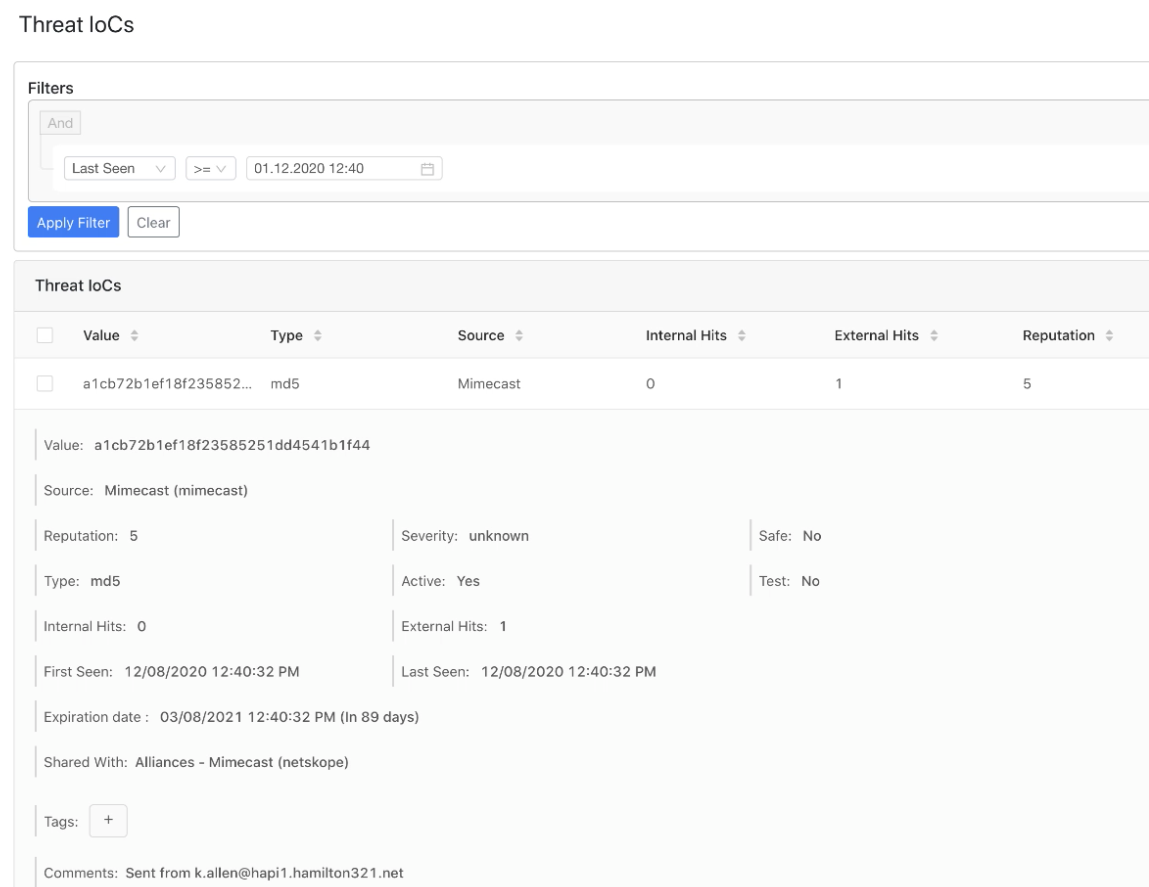
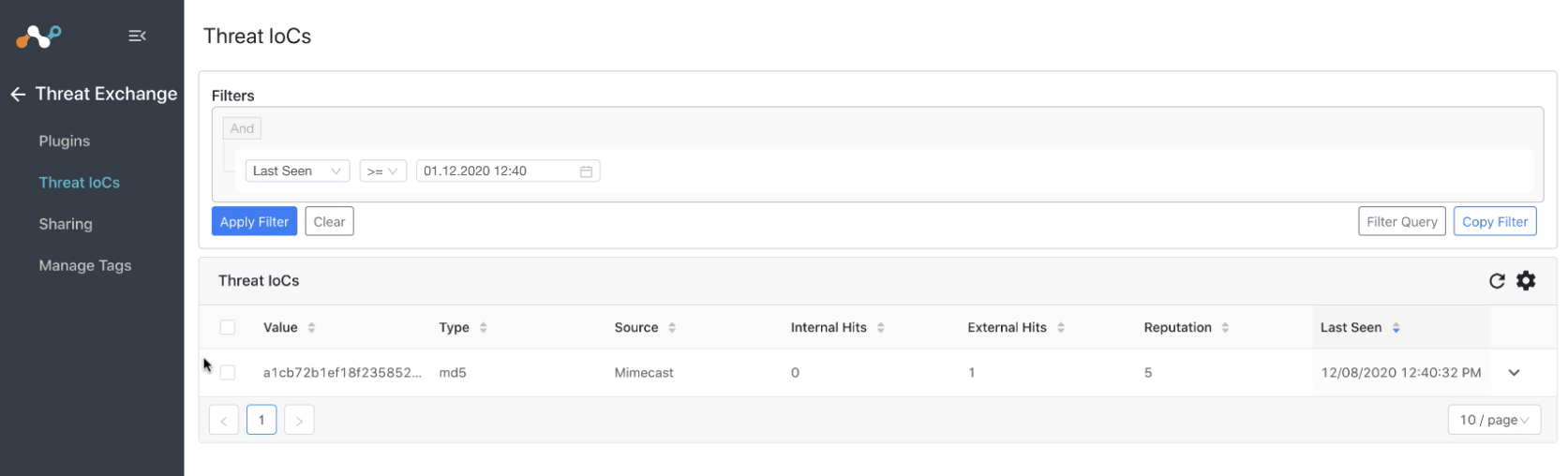
3. Key threat identifiers detected by Attachment Protection inspection funnel are shared with the Netskope platform.
4. Netskope uses this information in the threat detection service to block matching indicators downloaded from the web or uploaded to cloud services.
5. Key threat from the Netskope platform shared with Mimecast to provide consistent protection from threats, and automatically block future matching indicators.

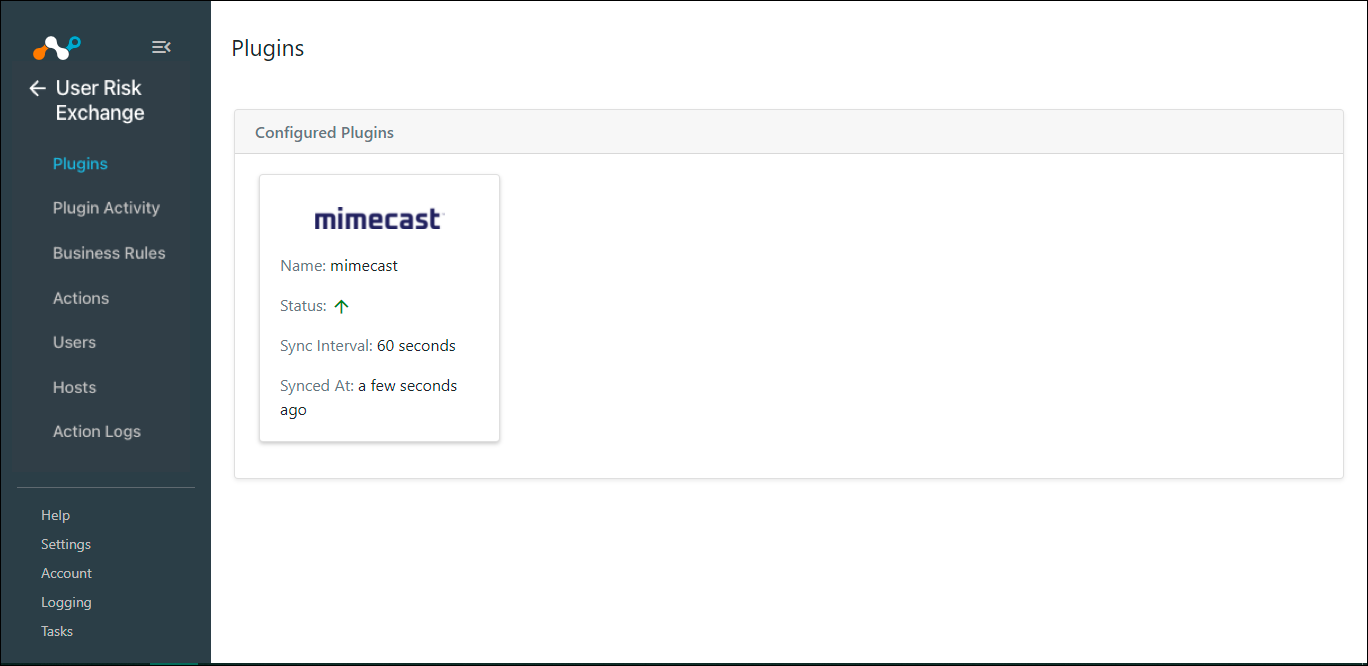
Simple Setup, Powerful Protection
Mimecast + Netskope Use Cases:
Mimecast and Netskope provide continuous protection through:
Advanced Threat Detection
Improve your organization’s security posture and detect threats by augmenting email security with SASE and web security.

Lateral Data Movement
Detect and follow attackers even as they switch IP addresses, devices or credentials.
Threat Intelligence
Understand how your organization has been targeted and what attacks have been blocked for better protection at the email perimeter and cloud services.

Key Benefits
01.
Threat protection for email, sensitive data, cloud applications, and web services.
02.
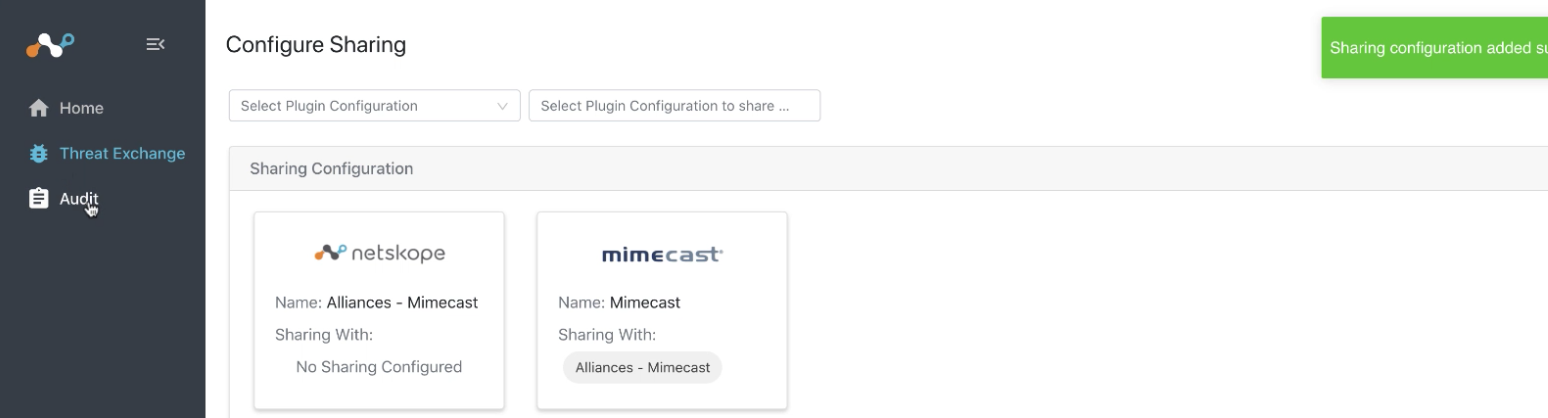
Bilateral threat exchange between Mimecast and Netskope.
03.
Deploy threat protection to detect and stop malware in storage apps
04.
Best-in-class shared intelligence preventing future attacks
Related Resources
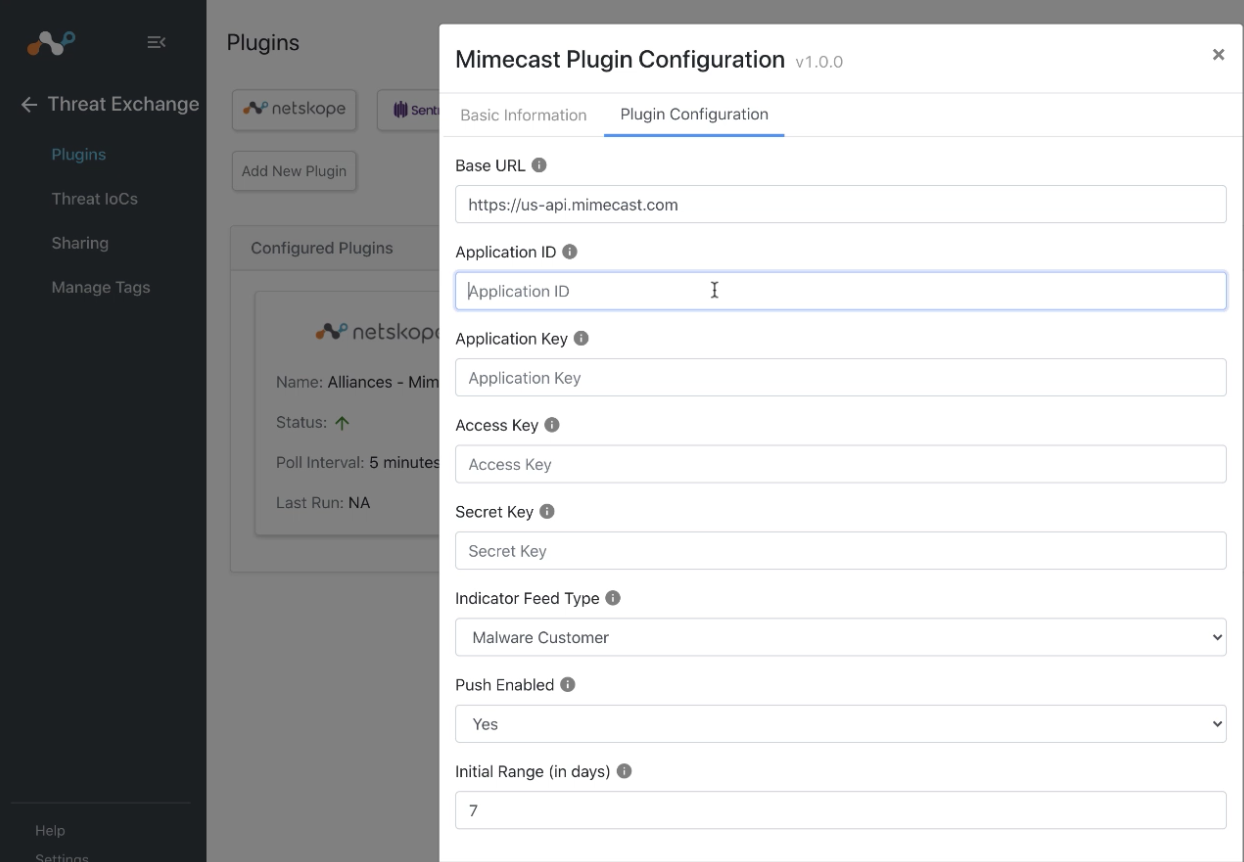
Netskope CRE
By integrating Mimecast with Netskope, security teams can leverage advanced threat detection, enhanced investigation and faster response to increase their overall level of protection through proactive actions that identify at-risk users and devices.